Advanced Dark Web Monitoring
The Dark Web features numerous marketplaces where emerging cyber threats are traded. By leveraging machine learning and natural language processing, Cyble efficiently connects Dark Web sites with other threat intelligence sources. This boosts your capability to promptly identify, assess, and mitigate risks affecting your organization.

What is Dark Web Monitoring?
Data brokers and cybercriminals regularly sell and exchange personal information on the dark web, making it challenging for security teams to monitor these forums and marketplaces. Dark web monitoring leverages advanced human and AI technology to gather and analyze raw data from the dark web in real time. This process involves scanning the dark web for information related to your organization, such as leaked or stolen data, compromised credentials, intellectual property, and other sensitive information.
Why Dark Web Monitoring Matters
Monitoring the dark web is a challenging and costly endeavor, necessitating ongoing data collection and intelligence gathering across hidden and clandestine platforms. It requires specialists who have infiltrated and established networks within these deep web communities to track channels such as TOR, I2P, ZeroNet, Telegram, Discord, and IRC. This insider knowledge enables organizations to detect credential theft and data breaches early, perform contextual analysis of cyber threats, and receive actionable alerts.
Utilize Dark Web Monitoring to detect potential threats early and identify exposed data
Leverage Dark Web Monitoring to Detect Threats Early and Uncover Leaked Data Before It Causes Damage
Dark Web Monitoring
Every day, cybercriminals upload millions of stolen user records, credit card details, intellectual property, and login credentials to the Dark Web.s
Threat Analysis
Cybercriminals leverage the Dark Web to orchestrate and execute social engineering attacks targeting key individuals and executives in organizations.
Early breach detection
Proactive breach detection enables security teams to reduce risk exposure, ensure physical safety, and mitigate damage from attacks.
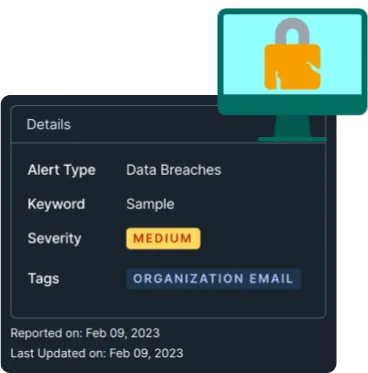
Data Breach Detection
Leverage insights from 350+ billion Darkweb records and 50+ billion threat indicators, covering 90% of the cybercrime landscape. Monitor 15+ billion pages daily using our patented NLP and ML algorithms for enhanced cybersecurity.
Early Alerts
Allocate essential time for your team to strategize the most effective asset recovery methods or secure them from cybercriminals before they can initiate attack plans.
AI Risk Tagging
Our AI-driven risk severity tagging identifies critical breaches early, keeping your data secure and inaccessible.
Cybercrime Forum Mentions
Access to a Cybercrime forum allows organizations to grasp the context of cyberattacks, receive actionable alerts, and respond swiftly.
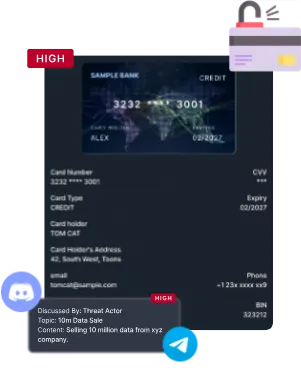
Compromised Cards Detection
Compromised Card Detection supports fraud prevention teams in identifying compromised credit cards through illicit channels or data breaches and in pinpointing high-risk merchants before fraudulent transactions occur or escalate.

Why Choose DefenceRabbit
DefenceRabbit's transparent, collaborative partnership helps uncover the real risks in your application. With extensive experience in application penetration testing, we offer clients precise insights and actionable solutions to safeguard critical assets. Our experts excel in:
Dedicated to Cybersecurity Excellence
We bring years of hands-on experience and a relentless focus on quality to every engagement, ensuring thorough and reliable security testing.
Safeguard Your Digital Assets
Our experts go beyond automated scans to uncover real threats helping you stay ahead of attackers and defend what matters most.
Data Privacy & Compliance
We help you meet stringent data protection regulations and industry standards, reducing your risk exposure and ensuring regulatory compliance.
Recognized Expertise
Our creative, adversarial engineers have decades of experience and unparalleled technical expertise in application penetration testing.
Proven Methodology
Whether you choose a framework-based or goal- based approach, we uncover the material risks that automated tools and buy bounty programs miss.
Innovative Enablement Platform
Our proprietary offensive security platform underpins every engagement to streamline collaboration and allow our expert engineers to focus on uncovering high value, material risks.
Enhance Your Business With A GCSS Cyber Security Services
Get in touch with our experts today
FAQ