Secure Software Development Life Cycle (SSDLC)
At DefenceRabbit, we understand that securing software is not just an afterthought it's a continuous process. That’s why we follow a Secure Software Development Life Cycle (SSDLC) approach, integrating security best practices at every phase of the SDLC. Our SSDLC methodology ensures that security is baked into your software from initial planning to deployment and maintenance, helping to minimize vulnerabilities, reduce risk, and ensure compliance with industry standards.



What is SSDLC?
The Secure Software Development Life Cycle (SSDLC) is a proactive security approach that transforms how applications are built and maintained, ensuring a security-first software development life cycle. Unlike traditional development practices where security is addressed only after deployment or worse, after a breach SSDLC integrates robust security practices at every phase of the Software Development Life Cycle (SDLC). By embedding security from the planning stage through development, testing, deployment, and maintenance, SSDLC ensures that security is not an afterthought, but a foundational element of the development process.
Creating a Secure Development Lifecycle in an Agile Organization
Incorporating a Secure Software Development Life Cycle (SSDLC) within an Agile framework is essential but often challenging; however, our services streamline this process. Agile emphasizes speed and flexibility, while security often demands careful analysis and rigorous validation. Bridging these two priorities requires a structured, yet adaptive, approach. Here’s how we help organizations embed security into their Agile development process:
- Empower Developers to Lead Secure Development
To build a secure foundation, we: • Clearly define security roles and responsibilities across development teams. • Deliver secure coding and code review training to upskill developers. • Establish and maintain secure code review checklists for consistent validation. • Guide the creation of an architecture vision that aligns with security best practices and compliance standards. Outcome: Developers become accountable for secure development from day one, creating a strong security-first mindset.
- Integrate Continuous Security into CI/CD Pipelines
Security must be continuous not an afterthought. We help you: • Integrate automated security tools like static code analysis and vulnerability scanners directly into the build pipeline. • Define security deliverables that act as quality gates: - Automated scan reports before minor releases - Manual penetration testing before major releases Outcome: Security checks are embedded into every iteration, ensuring continuous validation without slowing down Agile delivery.
- Evolve and Adapt: Keep Security Agile
Security must evolve with your Agile teams. To support this: • We facilitate ongoing security awareness training and knowledge refresh sessions. • Conduct security retrospectives and lessons-learned workshops post-deployment. • Maintain a centralized knowledge base for secure development practices, tool usage, and threat intelligence. Outcome: Your teams stay updated on the latest threats and best practices without disrupting Agile flow.
- Build a Culture of Security
By consistently applying the above practices, your team: • Establishes repeatable risk analysis and continuous integration practices. • Becomes familiar with security artifacts, such as checklists, metrics, and threat models. • Gains confidence in maintaining security compliance and best practices across the SDLC. Outcome: Security becomes second nature, not a burden.
- Embed Security in User Stories
Security starts at the story level. We ensure: • Every user story is analyzed from both a functionality and security perspective. • Security controls are designed to protect confidentiality, integrity, and availability (CIA) of sensitive data. • Story-level security measures are aligned with your broader architecture and risk management strategy. Outcome: Every sprint delivers not just features, but secure, resilient features ready for the real world.
Secure Software Development Life Cycle (SSDLC)
Secure Code Review & Analysis
Automated static analysis tools scan your codebase for vulnerabilities as part of our SSDLC services, while expert analysts perform manual reviews to uncover logic flaws. Early remediation ensures cleaner, safer code.
Vulnerability Management & Remediation
Continuous monitoring for CVEs and misconfigurations, with rapid patching and risk-based prioritization to reduce your attack surface and respond swiftly to threats.
Compliance & Regulatory Adherence
Align with standards like PCI DSS, HIPAA, GDPR, and ISO 27001 through our SSDLC compliance framework. We provide audit-ready documentation and help mitigate legal and financial risks from the start.
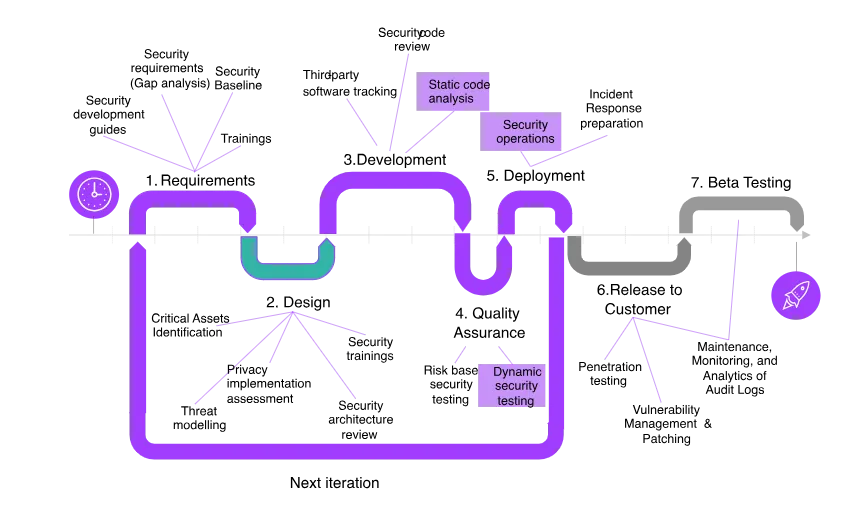
Our Secure Development Workflow
At DefenceRabbit, our proactive Secure SDLC workflow ensures that every stage of development is protected. We integrate security, compliance, and resilience into your entire software lifecycle.
FAQ