Faster, Easier, Affordable Compliance!

70%
lesser manual effort
 75+ integrations
75+ integrations Automated workflows
Automated workflows 50+ ready policy templates
50+ ready policy templates

~50%
reduction in the cost of compliance
 No hidden auditor or pen-test costs
No hidden auditor or pen-test costs Managed SLAs with auditors
Managed SLAs with auditors

< 6 Weeks
SOC 2 audit completion
 Implementation playbook
Implementation playbook Pre-mapped controls
Pre-mapped controls 24X5 Expert guidance
24X5 Expert guidance
Get SOC 2 compliant while you go about your day
We built DefenceRabbit to not just drive compliance but to ensure it. The platform does much of the heavy lifting so you do only the things that are necessary, never those that aren't. Trust DefenceRabbit to organize and track your compliance program(s) end-to-end.

We make audits more efficient and less of a hassle by implementing technologies and controls to meet each SOC 2 criteria. Our team will develop and manage an internal information security program that aligns with all SOC 2 controls and industry best practices. Post-report delivery, DefenceRabbit will continue to manage all controls to maintain compliance. Our security and compliance experts will guide you through each phase of the SOC 2 checklist.
Deliverables from DefenceRabbit
Our team is dedicated to delivering premium-tier service to ensure SOC 2 compliance. We customize and fulfill all items, from comprehensive data management plans, to fully itemized reports that provide information regarding methodology, findings, potential mitigations, and our recommendations.
DefenceRabbit specializes in enabling meaningful, real-world solutions to the most pressing challenges of the modern enterprise security environment. Assessment and reporting is contextualized to your business sector, and custom-tailored to your specific environment.
Our process is engineered to provide all the data and insights needed for you to make informed security decisions and take definitive action against unforeseen cyber threats.

A One-stop
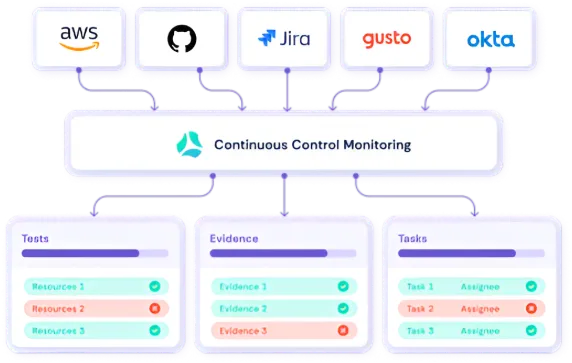
A SaaS platform powered by automation and integrations to help you consistently monitor and manage your tools, people & systems.
SOC 2
A Data Security audit issued by American Institute of Chartered Public Accountants (AICPA). This is required if you collect a client's confidential data, and make you business ready globally, especially to the US & EU.
Who needs itISO 27001
ISO/IEC 27701 is an extension of ISO/IEC 27001, providing a framework for establishing, implementing, maintaining, and continually improving a Privacy Information Management System (PIMS)…
Who needs itHIPAA
HIPAA ensures the security of confidential personal data associated with medical and healthcare streams. Ian other words any company that handles protected health information (PHI) should comply with HIPAA
Who needs itGDPR
GDPR is a EU regulation that protects the privacy and personal data of its citizens. Any business that collects the data of EU citizens must adhere to the GDPR.
Who needs itCost Calculator
Answer a few simple questions to help us understand what services you need, and our healthcare IT consultants will quickly get back to you to calculate a quote

Why Choose DefenceRabbit
DefenceRabbit's transparent, collaborative partnership helps uncover the real risks in your application. With extensive experience in application penetration testing, we offer clients precise insights and actionable solutions to safeguard critical assets. Our experts excel in:
Dedicated to Cybersecurity Excellence
We bring years of hands-on experience and a relentless focus on quality to every engagement, ensuring thorough and reliable security testing.
Safeguard Your Digital Assets
Our experts go beyond automated scans to uncover real threats helping you stay ahead of attackers and defend what matters most.
Data Privacy & Compliance
We help you meet stringent data protection regulations and industry standards, reducing your risk exposure and ensuring regulatory compliance.
Recognized Expertise
Our creative, adversarial engineers have decades of experience and unparalleled technical expertise in application penetration testing.
Proven Methodology
Whether you choose a framework-based or goal- based approach, we uncover the material risks that automated tools and buy bounty programs miss.
Innovative Enablement Platform
Our proprietary offensive security platform underpins every engagement to streamline collaboration and allow our expert engineers to focus on uncovering high value, material risks.