Cloud Penetration Testing
DefenceRabbit’s Cloud Penetration Testing services protect your cloud infrastructure against evolving cyber threats, leveraging deep industry expertise and proven penetration testing methodologies. Our experienced security professionals uncover a wide range of vulnerabilities including subtle, often-overlooked risks that automated scanners and less specialized teams may miss. With DefenceRabbit’s comprehensive testing approach, you can ensure your cloud environment remains secure, resilient, and compliant with best security practices.
Achieve Results with Efficiency and Efficacy
Analyze Your Cloud Environment Like an Experienced Attacker
Skilled cloud attackers think and operate with advanced tactics, often exploiting subtle vulnerabilities that others overlook. By simulating the methods of a proficient adversary, you gain critical insights into potential risks and vulnerabilities. This proactive approach helps you understand what could happen if a determined attacker targeted your secured cloud assets, allowing you to strengthen defenses and minimize the risk of a successful breach.
Customize Testing for Your Biggest Risk Scenarios
Tailor your penetration testing to evaluate defenses against your most critical threat scenarios. With a flexible approach, we focus on the specific techniques and vulnerabilities that are most relevant to your organization’s unique risks. This ensures a thorough evaluation, helping you identify and mitigate potential threats before they can be exploited.
Uncover Vulnerabilities: Essential Baseline Assessment Gaps
Focusing solely on misconfigurations leaves your organization exposed to significant risks. It’s crucial to uncover the full spectrum of vulnerabilities and potential internal pathways that attackers might exploit. A comprehensive baseline assessment goes beyond basic checks to identify hidden risks and strengthen your defenses across all layers of security.
Assess the Power of Your Cloud Security Measures
Your cloud security is only as strong as its weakest link. By evaluating your current defensive posture, you can uncover hidden gaps and strengthen protection against the latest cloud-based attacker tactics and techniques. A thorough assessment empowers your organization to proactively enhance resilience and stay ahead of emerging threats.
Concentrate Efforts and Resources for Maximum Impact
Time and resources are limited make them count. Prioritize your team’s efforts by focusing on the most critical vulnerabilities that are most likely to be exploited by attackers. By cutting through the noise and targeting high-impact issues, you can accelerate remediation and significantly strengthen your cloud security posture.
Forge a Path to Enhanced Cloud Resilience
Avoid recurring security gaps by building a smarter, stronger defense. Gain executive buy-in from key stakeholders to support strategic improvements that harden your cloud environment against future threats. With a focused, organization-wide approach, you can drive long-term cloud resilience and reduce risk across every layer of your infrastructure.
Reduce organizational risk and enhance cloud and container security
Organizations leveraging cloud and container technologies encounter unique security challenges that our Cloud Penetration Testing services are designed to tackle. Our Cloud and Container Security Penetration Testing Identifies Vulnerabilities in AWS, Azure, Google Cloud, and Containers That Could Compromise Your Security Posture.
AWS Penetration Testing
Identify gaps in S3 buckets, EC2 instances,and exposures in publicly accessible resources.
Azure Penetration Testing
Discover high-impact vulnerabilities in your Azure virtual machines, Azure Active Directory, and exposures in publicly accessible resources

Google Cloud Penetration Testing
Identify gaps in Cloud Storage, Google Compute Engines and exposures in publicly accessible resources.
Improve Container Security
Test deployments of AWS Elastic Container/Kubernetes Service, Azure Kubernetes Service (AKS), Google Kubernetes Engine.

Network Security
Check for legacy network protocols that are used by attackers to pivot and elevate privileges
OS and Third Party Patching
Check for gaps in your vulnerability management program
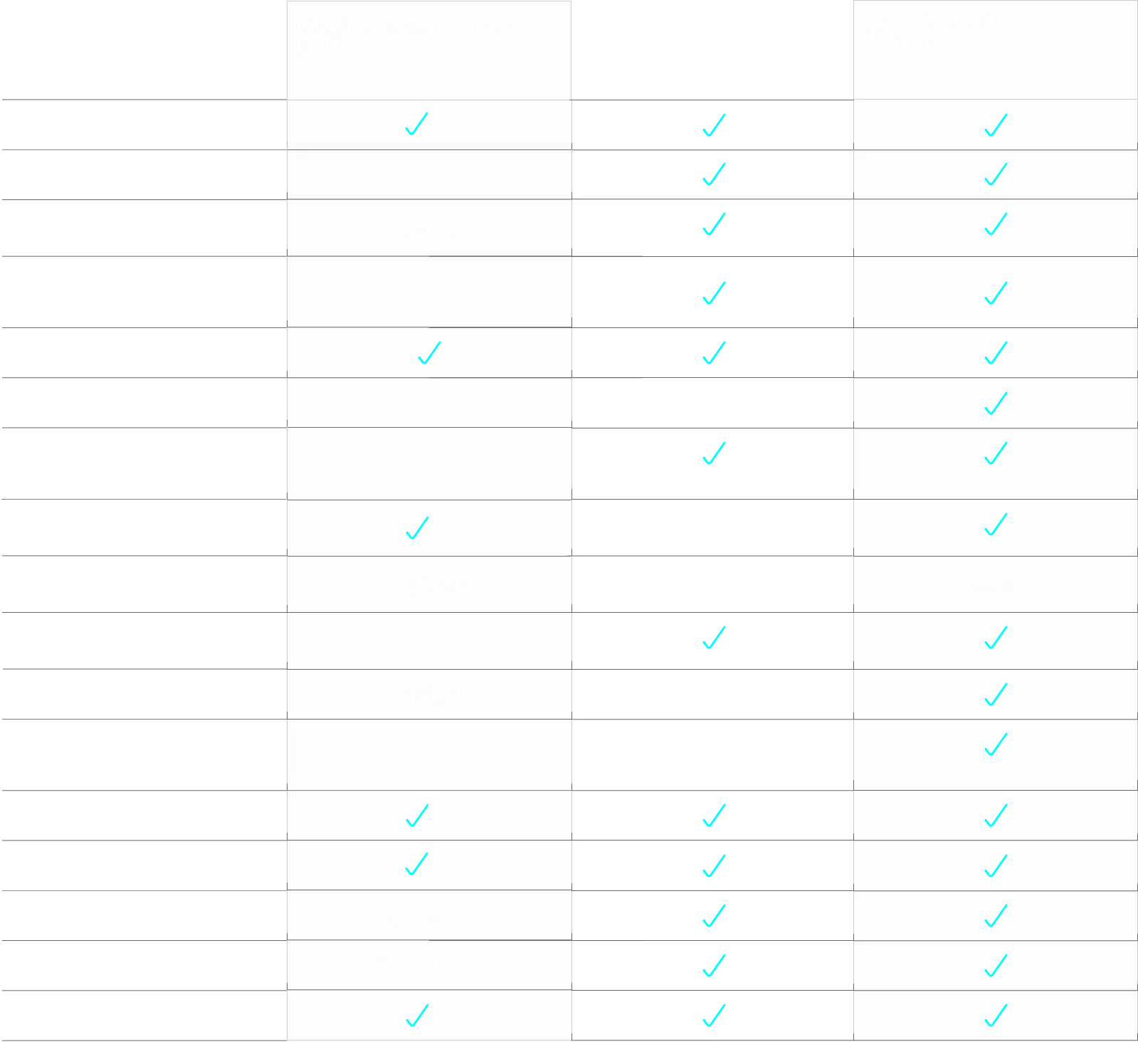
Cloud Penetration Testing Services Comparison
A comprehensive, adversarial-focused assessment of your web or cloud’s security posture.

Why Choose DefenceRabbit
At DefenceRabbit, we specialize in application penetration testing and web application security. Our transparent, collaborative approach uncovers real vulnerabilities, helping you secure your apps and comply with industry standards.
Dedicated to Cybersecurity Excellence
We bring years of hands-on experience and a relentless focus on quality to every engagement, ensuring thorough and reliable security testing.
Safeguard Your Digital Assets
Our experts go beyond automated scans to uncover real threats helping you stay ahead of attackers and defend what matters most.
Data Privacy & Compliance
We help you meet stringent data protection regulations and industry standards, reducing your risk exposure and ensuring regulatory compliance.
Recognized Expertise
Our expert penetration testers bring decades of experience and unmatched technical skill in application security assessments.
Proven Methodology
Whether you opt for a framework-based or goal-oriented strategy, we identify critical risks that automated tools and bug bounty programs often overlook.
Innovative Enablement Platform
Our cutting-edge cybersecurity platform enhances every engagement to boost collaboration and enable our expert engineers to identify critical, high-impact vulnerabilities.
Cloud Penetration Testing Deliverables
Executive Summary
Our cloud penetration testing deliverables include a clear and concise overview outlining the objectives of the engagement, key security findings relevant to infrastructure, and their potential business impacts. This summary highlights critical vulnerabilities, prioritized risks, and offers strategic recommendations to enhance your organization’s security posture. It serves as a high-level guide for executives to understand the value of the assessment and make informed, forward-looking decisions.
Engagement Outbrief Presentation
A structured, high-level presentation designed to mirror the executive summary, tailored for the audience of your choice whether executive leadership, technical teams, or stakeholders. This session summarizes the engagement objectives, key security findings, business implications, and actionable recommendations, providing clarity on outcomes and enabling informed decision-making across the organization.
Engagement Outbrief Presentation
A focused summary of the engagement, similar to the executive summary, tailored for delivery to your chosen audience. This presentation highlights key findings, business impacts, and strategic recommendations ensuring clear communication of results and supporting informed decisions across both technical and executive teams.
Ready to Discuss Your Attack Path Mapping Initiative?
DefenceRabbit's offensive security experts specialize in red teaming pen testing and simulated cyber attacks, ready to answer your questions and help improve your security posture.
FAQ